Protecting Critical Facilities
— The Concept of “Multi-layered Security” Seen in Power Plants —
Power infrastructure forms the backbone of modern society.
For this reason, power plants are classified as critical infrastructure, where intrusion, sabotage, or disruption must never be allowed, and an exceptionally high level of security is required.
However, no matter how advanced a sensor or surveillance system may be, a security design that relies on a single countermeasure always carries inherent risks.
What critical facilities truly require is not protection at isolated “points,” but a structured and systematic approach to defense.
This is where multi-layered security becomes essential.
It is a security strategy designed to minimize damage and ensure that critical assets are protected under all circumstances.

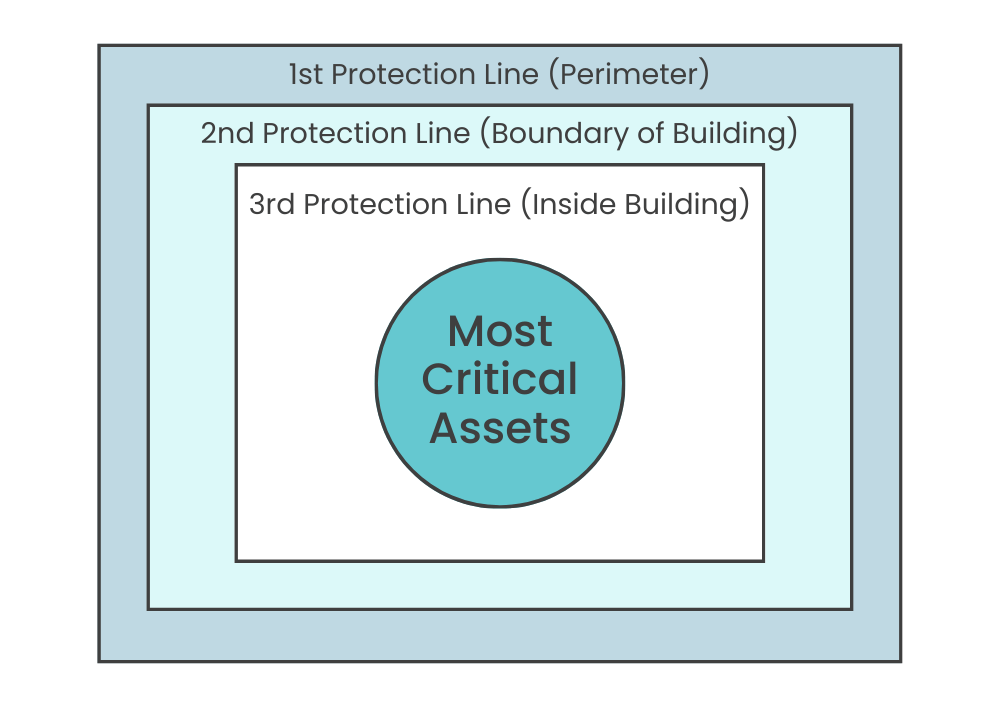
Designing Multi-Layered Security Through Protection Zones
The essence of multi-layered security in critical facilities is placing concentric layers of protection around the most critical assets that must be protected.
In the case of a power plant, the core assets include:
- Power generation equipment itself
- Control rooms and control systems
- Substations and other critical infrastructure equipment
These are assets whose loss would have an immediate and significant impact on society.
By defining them as the center and designing multiple protection lines around them, a true multi-layered security architecture is formed.
This zone-based design approach is the fundamental principle behind effective multi-layered security.
Protection Lines as a Nested Defense Structure
Using a power plant as an example, let us look at protection lines as a nested, concentric structure.
In this article, we organize the concept of multi-layered security based on this nested design, examining the roles and design principles of the 1st, 2nd, and 3rd Protection Lines.
In particular, the First and Second Protection Lines, which focus on outdoor protection, require a different perspective from conventional indoor detection.
Rather than detecting intrusions only after an attacker has entered a building, the key objective is to design a structure that prevents intruders from approaching the facility in the first place.
By combining early detection in outdoor areas with measures that deter or delay approach, a more robust and resilient multi-layered security architecture can be achieved as a whole.
(1) First Protection Line:Perimeter Protection
— Detecting Intrusions at the Earliest Stage —
In a multi-layered security design for power plants, the First protection line is the site perimeter.
Power plants typically cover large areas, making it structurally difficult to maintain constant human observation or visual monitoring along the entire perimeter.
This challenge becomes even more pronounced under conditions such as nighttime, poor visibility, or severe weather, where recognizing intrusions or abnormal situations is likely to be delayed.
Detecting an intrusion as early as possible has a significant impact on the overall effectiveness of security measures and the potential scale of damage.

At the perimeter, physical defenses such as fences and walls are commonly installed.
While these measures play an important role in deterring and delaying intrusions, they do not, by themselves, provide a means of detection.
For this reason, effective perimeter protection requires a combination of physical boundaries and detection technologies.
By identifying intrusions or suspicious activity at an early stage and passing that information on to the next protection line, the foundation of a robust multi-layered security system is established.
OPTEX Perimeter Protection Solutions
OPTEX’s Perimeter Intrusion Detection System (PIDS) is an approach that enables early detection of unauthorized intrusions through sensors installed along the perimeter, and links detection events with video surveillance and security operations. This allows verification and initial response to be triggered directly from detection.
For this reason, the perimeter protection line is designed by selecting and combining single or multiple detection technologies, depending on surrounding environmental conditions, fence structures, and site characteristics.
Typical detection methods include:
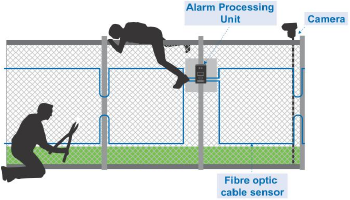
● Fiber Optic Sensors
They detect abnormal activity associated with intrusion attempts—such as climbing, crawling under, or cutting the fence—and are suitable for long-distance perimeter sections.
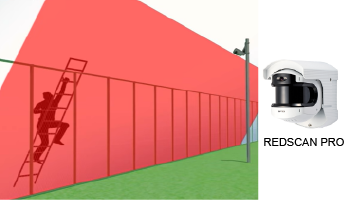
● LiDAR Sensors
By capturing areas in two dimensions, they can identify a target’s size, speed, and distance, enabling reliable detection of human and vehicle movement.
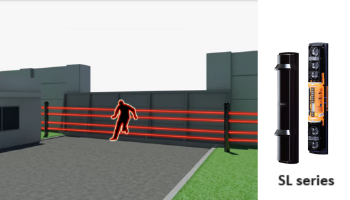
● Photobeam Sensors (Active Infrared)
(2) Second Protection Line:Inside the Perimeter ~ Around Buildings
— Capturing Intruder Movement and Location —
It is essential to establish a second protection line inside the perimeter in preparation for the possibility that the first protection line may be breached.
The second protection line functions as the last outdoor layer of defense before an intruder can reach internal facilities, and it has a significant impact on the overall security of the site.
Areas inside the perimeter and around buildings represent the stage at which an intruder is moving toward their target.
The role of the second protection line is therefore not limited to simply confirming the presence of an intrusion, but also to reliably capturing the intruder’s location, movement, and approach after entry.
OPTEX Solutions for the Second Protection Line
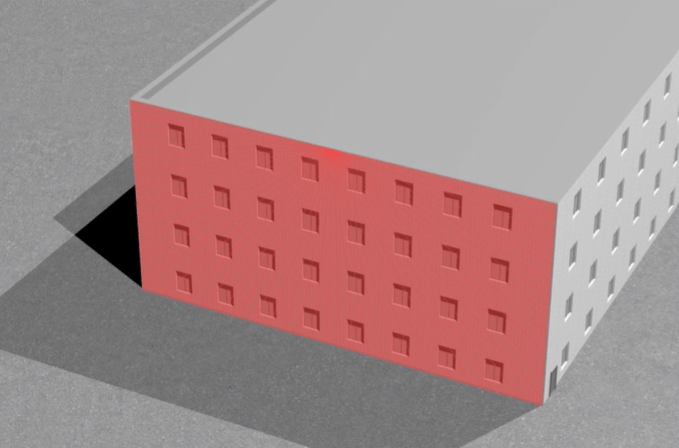
For areas inside the perimeter and around buildings, sensor configurations that can accurately detect intrusion and approach on an area basis are highly effective. For this purpose, OPTEX’s LiDAR sensor REDSCAN enables the design of detection areas tailored to building surroundings and movement paths, allowing reliable detection of intrusion and approach.
REDSCAN can identify a target’s size, speed, and distance. By combining these capabilities with zone-based design and clearly defined alarm conditions, it is possible to generate alerts that are essential for response decisions while reducing the operational burden caused by false alarms.
Another key advantage of REDSCAN is its flexibility in configuring detection zones for areas that tend to become blind spots for cameras, such as inside fences or around buildings.
Furthermore, by integrating sensor detection with CCTV, alarms can be used as triggers for immediate visual verification.
This supports early recognition of emergency situations and enables faster, more informed decision-making by security operators.
Vertical Detection Area
Horizontal Detection Area
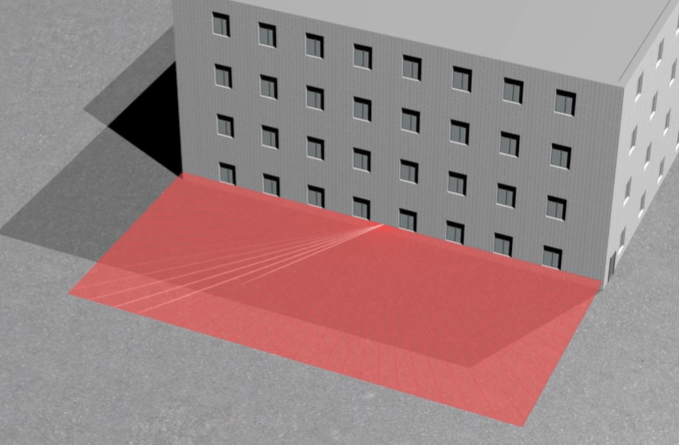
Image of LiDAR sensor in Substation

(3) Third Protection Line:Indoor Protection
— Ensuring Reliable Detection of Intrusions into Critical Rooms —
The Third protection line is the innermost defense layer in a multi-layered security design for power plants.
Its role goes beyond simply detecting the presence of an intruder inside a building. It is designed to maintain a state in which unauthorized individuals are prevented from reaching or interacting with critical areas, such as control rooms, electrical rooms, and communication rooms.
When designing the 3third protection line, it is essential to select the most appropriate sensor technologies based not only on the criticality of each area, but also on environment-specific factors that may cause false alarms.
For general indoor intrusion detection, PIR (Passive Infrared) sensors are widely used.
In critical facilities, however, dual technology sensors—which combine PIR and microwave detection—are often adopted to enhance detection reliability while minimizing false alarms.
In particularly sensitive areas such as control rooms, electrical rooms, and communication rooms, a more robust boundary protection strategy can be achieved by combining sensors according to the application, as described below.
● LiDAR Sensors
By configuring the detection area vertically, a virtual laser wall can be created, enabling area-based detection of intrusions into restricted zones.
When configured horizontally, LiDAR sensors can also detect intrusion routes that are difficult to monitor, such as ceiling voids or underfloor spaces.


● Photobeam Sensors (Active Infrared)
By protecting areas in front of critical equipment or along windows as linear detection zones, they enable precise identification of where an intrusion occurs.
OPTEX Solutions for the Third Protection Line
OPTEX offers a comprehensive range of indoor intrusion detection sensors—including PIR, dual technology, Active Infrared and LiDAR sensors.
These solutions can be integrated with VMS and NVR systems, supporting reliable detection, visual verification, and coordinated security operations within critical facilities.
Conclusion: The Multi-Layered Security Approach Required for Critical Infrastructure
Multi-layered security in physical protection for critical facilities is a security strategy that designs multiple protection layers—from the perimeter to the area around buildings and into interior spaces—in order to progressively reduce risk.
Even if one protection line is breached, the objective is to contain the risk at the next layer and prevent escalation or widespread damage.
By appropriately designing the outdoor protection lines, represented by the First and Second protection lines, it is possible to achieve early detection and accurate situational awareness while minimizing false alarms.
Based on this multi-layered security philosophy, OPTEX provides solutions centered on consistent intrusion and approach detection from outdoor to indoor areas.
Through this approach, OPTEX supports the construction of security architectures for critical facilities that deliver the required levels of safety, operational efficiency, and long-term reliability.
Contact OPTEX
Please feel free to contact us for further information.
We are always eager to support you and propose a solution that suits your needs.